- 164 Posts
- 1.13K Comments

 12·3 days ago
12·3 days agoThis tool looked interesting to me until I noticed that its external dependency count is in the hundreds, each of which increases exposure to vulnerabilities and supply chain attacks.
I hope that Rust will some day have a rich enough standard library that the “trust everything” software development model falls out of favour amongst the developers who use it.

 7·4 days ago
7·4 days agoYou might start with the documents posted to the EFF site over the past year. For example, the September opposition letters include specific court decisions and put them in context, including commentary from law professors.

 11·5 days ago
11·5 days agoLooks like things have changed:
Will my registration expire?
No, your registration will never expire. The FTC will only remove your number from the Registry if it’s disconnected and reassigned, or if you ask to remove it.
https://consumer.ftc.gov/articles/national-do-not-call-registry-faqs

 14·5 days ago
14·5 days agoIt’s re-posted from a news community, where it was since removed for not being from an acceptable news site. Unfortunately, the acceptable news sites covered this more than 30 days ago, which disqualifies their articles regardless of whether they were ever posted to the community. shrug
I couldn’t find a better article in the time I had to spare, so I re-posted this one. I think what’s important in this case is just that word gets out. I don’t see anything misleading about this one, and the EFF link (which is also not exactly a news site) is plainly visible.

 16·5 days ago
16·5 days agoSome of the APIs in use on Linux today come from older Unix variants. (For this reason, I probably wouldn’t call one of these a “Linux API” as the author did, though I guess it works linguistically for those that are usually present on Linux.) These APIs have semantics that were designed before threading existed on many platforms. Making them thread-safe without breaking existing code can be challenging.
If
setenv(3)is among these, it could explain why glibc’s implementation doesn’t support multi-threaded programs, and why its documentation states as much. To have used it in a multi-threaded environment, ignoring the docs, was a bug in the Steam client. Perhaps it never occurred to the people who ported Steam’s code to glibc that threading issues might be different from what they were used to on other platforms.To be fair, the author might be aware of this, as he did refer to glibc’s implementation as a tradeoff rather than a bug.

 39·6 days ago
39·6 days agoMatrix messaging apps. It’s nice to have modern messaging features, end-to-end encrypted, with no single point of failure, no Google involvement, and no phone numbers. I expect to start recommending it widely when the 2.0 features land in the popular clients.
WireGuard VPN. It’s fast, even on low-power devices.
Self-hosted Mumble. Excellent low-latency voice quality for chatting or gaming with friends.
Radicale, DAVx⁵, and Thunderbird, for calendar and contact sync between mobile and desktop, without handing the data over to Google or anyone else.

 7·8 days ago
7·8 days agoI don’t know of a universal tool for adding keyboard navigation to all the different GUI toolkits used on Linux. I wouldn’t expect one to exist, since each toolkit implements its widgets differently, just as the Windows and MacOS GUIs implement theirs differently.
However, apps made with Qt tend to be good at keyboard navigation already, which is no surprise, since support for it is built in to the toolkit. The KDE Plasma desktop environment inherits this support, as do most of the apps made for it. I suggest trying it if you haven’t already. (Hint: Many widgets will reveal their keyboard shortcuts when you hold down Alt, and a Settings: Configure Keyboard Shortcuts menu item is very common in KDE apps.)
Tangentially related: You might also want to look at tiling window managers. Some people love them.
Thorin has my respect for building his own machine.
I hope he saves the box for you.

 23·9 days ago
23·9 days agoCloudflare is a provider that you can choose to have as a part of your own infrastructure.
Indeed.
man in the middle implies “attack”
That can be a convenient shorthand if the parties in a discussion agree to use it as such in context. For example, in a taxonomy of cryptographic attacks, it would make sense. It is not the general meaning, though, at least not a universally accepted one. Similarly, “counter” does not imply “counter attack”, unless we happen to be discussing attack strategy.
More to the point, nothing that I wrote misrepresents the situation as was claimed by that other person. If I had meant attack, I would have said attack. Rather, they made a leap of logic because I (like most of my colleagues) don’t happen to follow a convention that they like, and picked a fight over it. No thanks.

 110·10 days ago
110·10 days agoYou’re conflating MitM,
Heh… It’s safe to assume I’m well versed in this topic.
You’re going to have to prove any of your claims, or else I am just going to assume you’re talking out of your ass.
I am not, however, inclined to indulge rudeness. Bye bye.

 138·10 days ago
138·10 days agoIt bugs me when people say Cloudflare is a MitM, because that is a disingenuous representation the situation.
No, it is a clear description of what is happening: Instead of https keeping the traffic encrypted from user to service, it runs only from user to Cloudflare (and then in some cases from Cloudflare to service, although that’s irrelevant here). The result is that a third party (Cloudflare) is able to read and/or modify the traffic between the two endpoints. This is exactly what we in mean in cryptography discussions by man-in-the-middle.
You can decide that you don’t mind it because it’s not a secret, or because they haven’t been caught abusing it yet, but to say it’s not a man-in-the-middle is utter nonsense.
and you opt into it.
No, the service operator opts in to it, without consulting the user, and usually without informing them. The user has no choice in the matter, and typically no knowledge of it when they send and receive potentially sensitive information. They only way they find out that Cloudflare is involved is if Cloudflare happens to generate an error page, or if they are technically inclined enough to manually resolve the domain name of the service and look up the owner of the net block. The vast majority of users don’t even know how to do this, of course, and so are completely unaware.
All the while, the user’s browser shows “https” and a lock icon, assuring the user that their communication is protected.
And even if they were aware, most users would still have no idea what Cloudflare’s position as a middleman means with respect to their privacy, especially with how many widely used services operate with it.
To be clear, this lack of disclosure is not what makes it a man in the middle. It is an additional problem.
it cannot be a MitM because both sides of the connection are aware of this layer.
This is false. Being aware of a man in the middle and/or willingly accepting it does not mean it ceases to exist. It just means it’s not a man-in-the-middle attack.

 11·10 days ago
11·10 days agoI think zero RPM worked before (on cards that supported it) but wasn’t directly configurable in Linux.

 1·10 days ago
1·10 days agoMy condolences. Unfortunately, people are sometimes designated the in-house expert on a thing just because they seem slightly less ignorant of it than anyone else in the organization. That leaves more than a few people making decisions that impact security and privacy without good understanding or sound judgment in those areas.
Maybe you should train up and become your state’s new security expert?

 2·10 days ago
2·10 days agoIt doesn’t necessarily mean putting it in a game’s launch options. Environment variables can be set in a startup script, or a flatpak config, or a command line, for example. But the Steam launch options approach is convenient when you’re just testing something for one specific game.

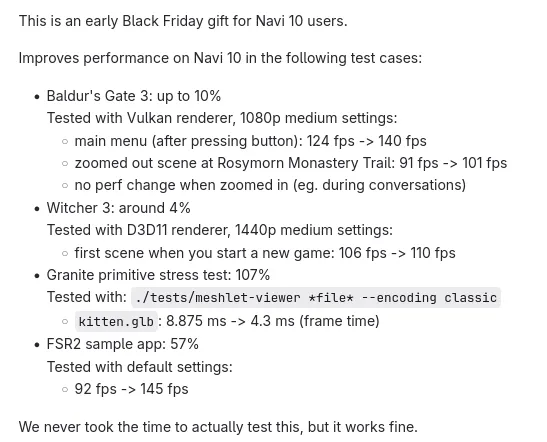
 505·10 days ago
505·10 days agomusic group IFPI complained that while Cloudflare discloses the hosting locations of pirate sites in response to abuse reports, it doesn’t voluntarily share the identity of these pirate customers with rightsholders.
“Where IFPI needs to obtain the customer’s contact information, Cloudflare will only disclose these details following a subpoena or court order – i.e. these disclosures are mandated by law and are not an example of the service’s goodwill or a policy or measures intended to assist IP rights holders,” IFPI wrote.
So the corporations enjoying enormous profits from other people’s work are unhappy that Cloudflare doesn’t make it easy for them to circumvent due process. What a surprise.
(I’m generally not a fan of Cloudflare, because its man-in-the-middle position between users and services has grown to an unhealthy scale, making it ripe for dragnet surveillance and other abuses. But it would be even worse if it was actively helping these greedy, predatory corporations dodge the law.)
They’re not saying it was unavoidable random chance. That’s not what perilous means.
They’re saying the consequence of the choice is peril, and they seem to agree with you about the would-be dictator:
He showed us in his first term and in the years after he left office that he has no respect for the law, let alone the values, norms and traditions of democracy. As he takes charge of the world’s most powerful state, he is transparently motivated only by the pursuit of power and the preservation of the cult of personality he has built around himself.

 2·11 days ago
2·11 days agoI would definitely try it. If it doesn’t help any game, or if it causes glitches/crashes, an environment variable is easy to revert.

 7·12 days ago
7·12 days agoI built a new machine pretty recently, also with an RX 7800XT GPU (factory overclocked). When sitting idle at the desktop, the system draws about the same amount of power as my old machine did with an RX 480. So I think trying to put the big GPU to sleep during desktop use might be barking up the wrong tree.
I suggest getting a power monitor, like a Kill-A-Watt, and taking measurements while you experiment. Here are some ideas to consider:
- Are you using multiple monitors? I have read that newer AMD GPUs sometimes draw more power than they should in this case. It might depend on the resolution and/or windowing system in use. (I don’t remember if the reports I read were on Wayland or Xorg.) It almost certainly is a driver issue.
- Are you using nonstandard timings? Have you tried different refresh rates? https://community.amd.com/t5/graphics-cards/which-monitor-timing-parameter-allows-gpu-vram-frequency-to/td-p/318483
- Have you been playing games for hours every day, with no frame rate limit? The graphics card can draw considerably more power pushing polygons at 1440p@180Hz than it does at 90Hz, for example, and I don’t think the wattage progression from idle to full load is linear.
- Are you using recent kernel and firmware versions?












What do these professions have in common? Requirement for a government-issued license?